According to independent researcher Gal secure Beniamini an attacker could easily break the encryption of disk relateif Android devices that are powered by a Snapdragon Qualcomm soc. The Full Disk Encryption (FDE) standard uses randomly selected 128-bit Device Encryption Key (DEK), which is further encrypted by the PIN code of the user, a password or a dot pattern.
Android uses DEK to encrypt files that are stored on a smartphone or tablet. The PIN or password, ensure additional protection of the DEK, because the attacker can decrypt files without thereby gain access to the device using one of the methods just mentioned.
Device Encryption Key, the key to all data is stored in the KeyMaster module, an area of Android’s TrustZone. This special section of the Android kernel, which operates separately from the rest of the kernel, and responsibility is to perform sensitive operations, such as the encrypted data on a smartphone or tablet.
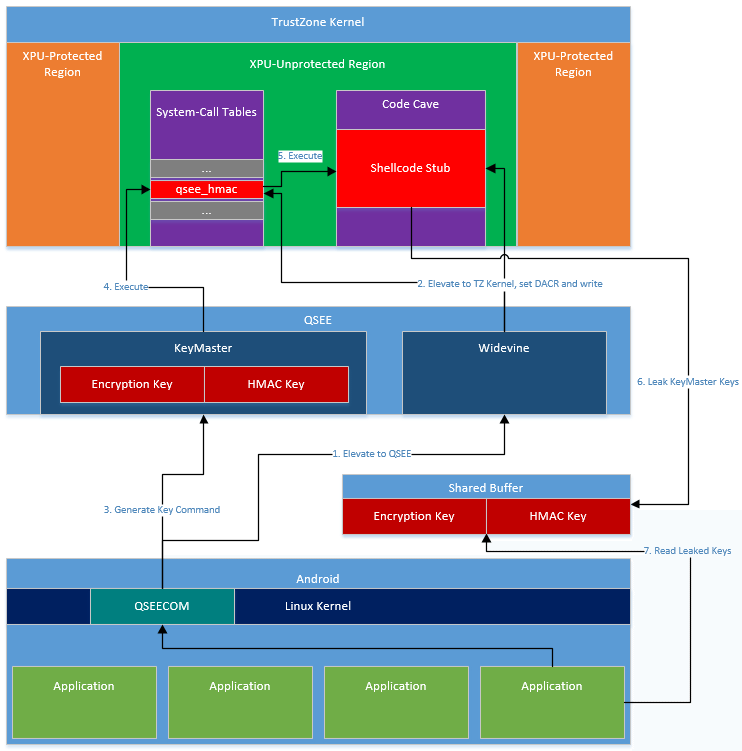
on Android devices with a chipset from Qualcomm does this in a different way, the KeyMaster module is in fact not implemented in the Trusted Zone, but in the Secure Execution Environment Qualcomm, an alternative to devices that use a Qualcomm Snapdragon sOC.
Beniamini claims that several vulnerabilities have been found for the Secure Execution Qualcomm Environment, which are used to extract the contents from the KeyMaster module. The researcher says he can load a malicious app in the QSee which he has control over the entire component. In this way, he can steal the Device Encryption Key because it is not linked to the hardware and therefore is also a brute-force attack possible.
A brute-force attack is simply trying all possible combinations until the right one is found. Beniamini itself created a Python script only 88 lines which is able to crack the Device Encryption Key through brute force, then the files of a user can be unlocked and used. The script is available on GitHub.
Unfortunately, the problem can not be solved with a software update, because Qualcomm have to change the design of the chips. At this time, all existing devices vulnerable to the attack just described
.
No comments:
Post a Comment